A New Era of Security
Thinking of revamping your vulnerability management program/process? Or looking to better develop and execute your risk management strategies and programs? 20 minutes of your time to discuss your security/compliance needs is all we need to understand your priorities.


About
Security Services & Solutions
Tier 3 Security is a premier cybersecurity service provider, our core approach is to align organization goals with IT by reducing vulnerabilities and ensuring compliance with standards which results in reducing the overall impact of attacks to your organization. We offer professional services (network and application pen-testing, risk assessments, vulnerability management, compliance engagements etc.)
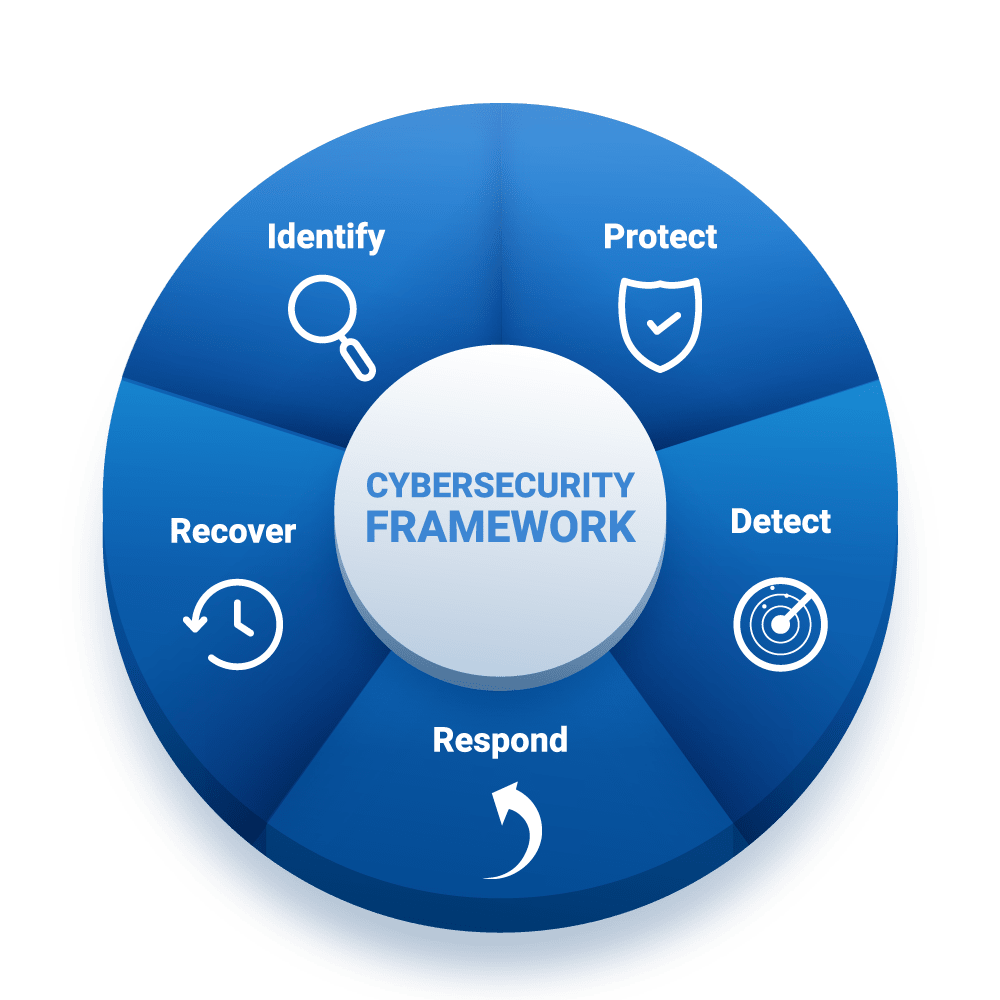
Cybersecurity Framework
The Cybersecurity Framework provides guidance for the process of identifying, assessing, and managing cybersecurity risk in a cost-effective manner based on business needs. This approach of cybersecurity risk management can be actively used by large- and medium-sized companies to protect their infrastructure from cyber attacks.
Features
What We Offer
We help you stay secure. We’re like your personal cyber security experts, helping you to stay safe online and battling malware, cyber hackers, and other web rascals seeking to harm you or your business.
Compliance
Compliance is ensuring that due diligence and care to protect the confidentiality, integrity, and availability of critical business assets, and data are implemented at all times. Tier 3 would ensure this by leveraging different frameworks such as but not limited to NIST, PCI DSS, HIPAA, and ISO 27001.
Risk Management
Risk management is a structured, consistent, and continuous process applied across an entire organization that allows companies to better understand and address material risks. The implementation of risk management can facilitate better capital resource allocation decisions, increase operational efficiency, and enhance a company’s risk control efforts to support critical strategic, compliance, and governance initiatives.
Vulnerability Management
Penetration Testing
Simply put, penetration testing is an offensive testing strategy that focuses on prevention. Tier3 Security can help identify weaknesses, vulnerabilities, and exploitable flaws within your network to prevent cyber-attacks.
Contact Us
info@tier3security.com
7307 Quartz Terrace, Bowie, MD 20720-4318
Monday-Friday: 8am - 5pm
Get Started
If you have any comments or questions about our services, click the button below to schedule a consultation.
